DoD photo by Sgt. Aaron Hostutler USMC
Spared from Hagel’s Cuts: Cyber, Asia-Pacific, Homeland Policy Jobs
Defense Secretary Chuck Hagel is cutting 200 jobs from his front office – but he made sure to protect several key policy positions in homeland, cyber and the Asia-Pacific. By Stephanie Gaskell
Defense Secretary Chuck Hagel just announced plans to trim his staff by about 200 positions over the next five years. But inside the secretary’s top policy shop, a closer look at the planned cuts show where Hagel’s priorities lie after more than a decade of war.
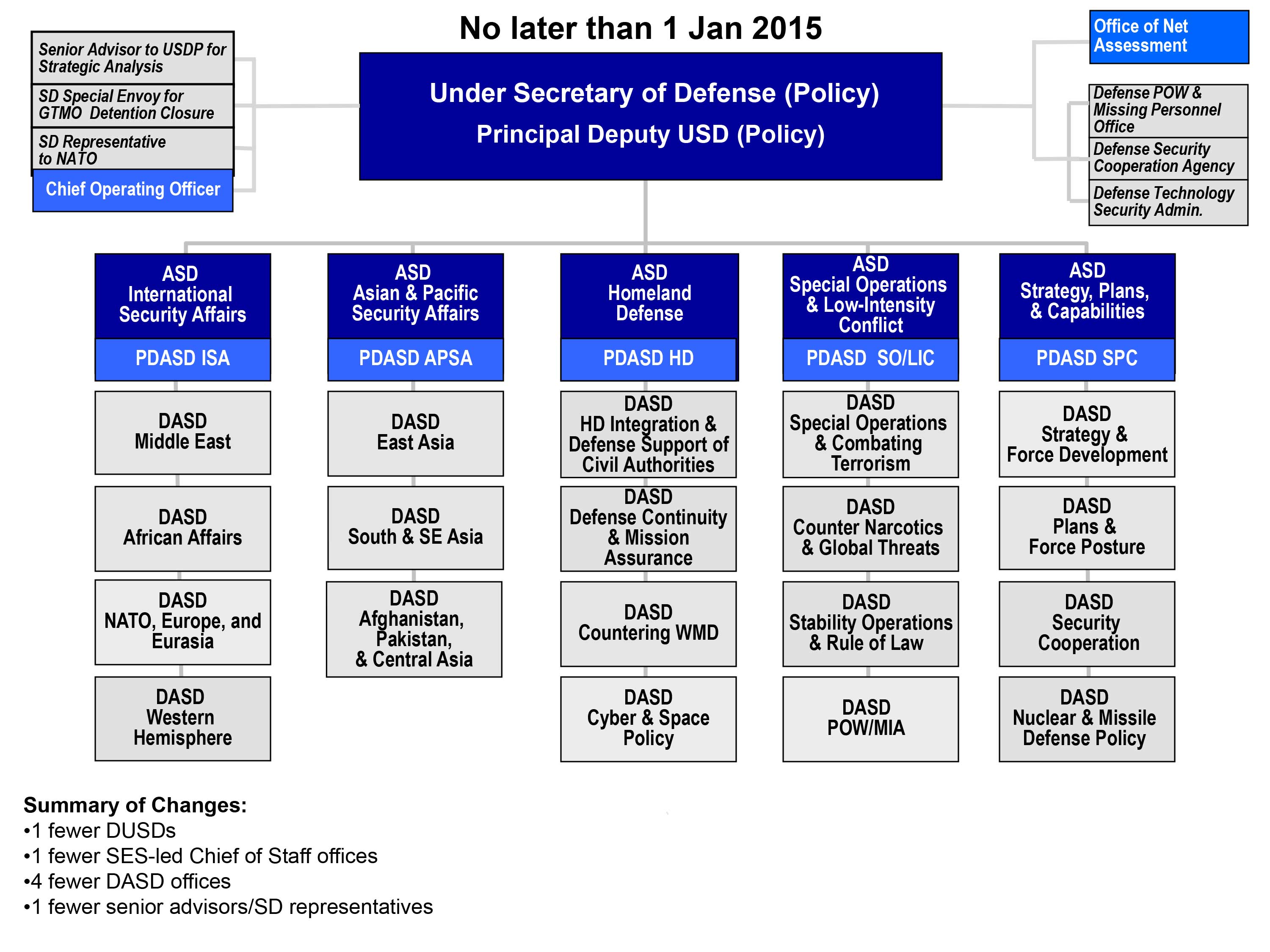
In the office of Under Secretary of Defense for Policy Jim Miller, Hagel is making sure to protect several key areas, namely homeland defense, cyber threats and the pivot to the Asia-Pacific region. Miller, who spoke to a small group of reporters at the Pentagon on Thursday, said despite the budget crunch, key policy areas were protected, including outer space threats and countering weapons of mass destruction. The Homeland Defense and Americas' Security Affairs units will actually be beefed up in the restructuring. “The reality is that the world has changed since 2009 when the current structure was put in place,” Miller said.
Joint Chiefs Chairman Gen. Martin Dempsey stressed during a Pentagon briefing on Wednesday the importance of Homeland Defense in the coming years. “The homeland is actually achieving greater prominence in our discussions of future strategy than at any time in my forty years, as it should,” he said.
Miller’s office has about 500 active-duty military and civilian employees. It will reduce its civilian and active-duty military personnel by 12 percent and reduce its contract support by about a third by fiscal year 2019.
Miller also said it will be crucial to work more closely with allies and partners, who are also doing more with less. “As we see our budgets shrinking, as we see our allies and partners, many of their budgets shrinking as well, the need to really think of security cooperation as driving strategy is even greater than it has been in the past,” he said. Miller has already announced he will step down next month after five years at the Pentagon.