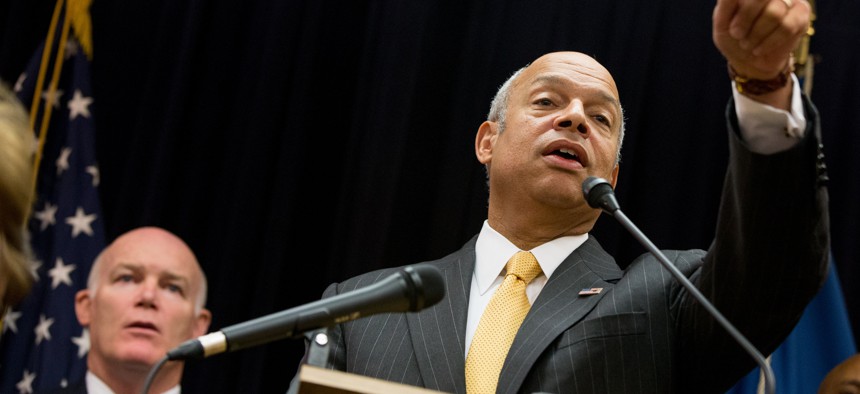
Homeland Security Secretary Jeh Johnson takes questions from members of the media following an event in Washington, Monday, Oct. 5, 2015, to thank Homeland Security Deparment employees for their work. AP Photo/Andrew Harnik
In Chattanooga’s Wake, DHS Wants To Revive Terrorism Alert System
With terrorist-inspired attacks on the rise, the federal government may revise the unused successor to the Bush-era color alerts.
President Barack Obama’s top homeland security official has ordered a review of the nation’s terrorism alert system to reflect what he called the growing threat of attacks originating within the United States.
The U.S. has never used the National Terrorism Alert System, a two-level system that replaced the oft-derided color-coded terrorism alerts installed after 9/11 to spread the word about potential attacks from abroad. But after a “homegrown violent extremist” killed five service members in Chattanooga, Tenn. — and amid the expectation of more terrorist-inspired attacks — the Department of Homeland Security wants to revise and jumpstart the system.
“I’ve asked our folks to consider whether we should revise that system to accommodate how the terrorism threat has evolved,” DHS Secretary Jeh Johnson said Tuesday at the annual meeting of the Association of the U.S. Army in Washington, D.C. “That review is underway now.”
Instead of the post-9/11 green-to-red progression, the NTAS has just two states of alert. An “elevated threat” means there is a credible threat against the United States. An “imminent threat” alerts the public to just that, “a credible, specific, and impending terrorist threat against the United States.”
Under the old system, DHS took much criticism that the nation was being held on constant orange alert for no good reason. But the department has since been criticized for never issuing any alerts. U.S. intelligence and national and local law enforcement officials have opted to keep the public in the dark to avoid panic with a sudden terrorism alert.
The review is the latest of several new security measures DHS enacted since last year to address the growing threat of terrorism that originates within the borders of the U.S., rather than from abroad.
"There is a new reality,” Johnson said at AUSA. “The global terrorist threat has evolved from terrorist-directed to terrorist-inspired attacks," he said.
Johnson also highlighted the department’s focus on stopping foreign fighters from entering the U.S., particularly through via the 38 Visa Waiver countries where so many have originated.
Later, Johnson was asked to assess how DHS would handle the coming influx of up to 10,000 Syrian refugees in this fiscal year. Johnson said the department has improved its ability to vet them using intelligence databases while meeting international commitments with the United Nations.
“We want to do more; we believe we need to do more,” he said. “I’m committed to doing that and to ensuring that those that are resettled are vetted property and receiving the appropriate security review.”
“We’ve gotten better at that over the last couple of years, but it is a time-consuming process and one of the challenges that we’ll have is that we’re not going to know a whole lot about the individual refugees that come forward.”