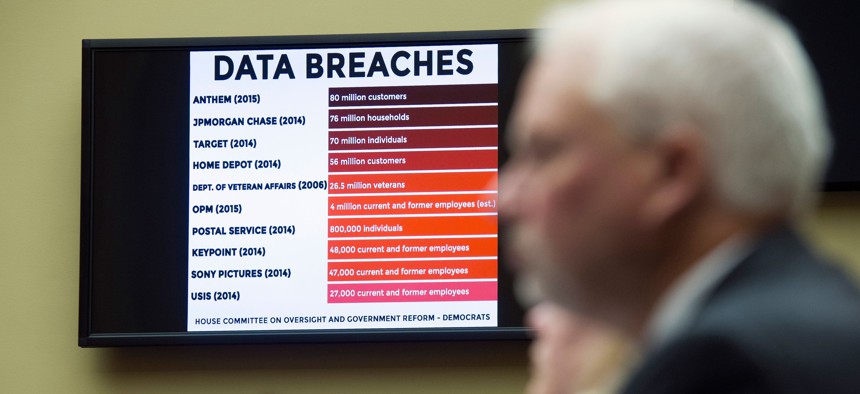
A chart of data breaches is shown on Capitol Hill in Washington, Tuesday, June 16, 2015, as witnesses testify before the House Oversight and Government Reform committee's hearing on the Office of Personnel Management (OPM) data breach. Cliff Owen/AP
Why the US Hasn't Pinned the OPM Hack on China
Getting China to stop this activity is at the top of Washington's diplomatic agenda. Stopping foreign intelligence services from spying, however, is not.
The theft of data from the Office of Personnel Management (OPM) has made great fodder for two weeks of cable news. Banner headlines have declared it an act of cyber warfare carried out by the Chinese government. Yet, while Twitter has been abuzz, official statements attributing the attack have yet to materialize.
There are two likely explanations for why the White House has not pinned the incident on China. The first possibility is that the evidence is not there yet. Given time, attribution may get to the point at which a public accusation would be warranted. A more intriguing option is that the administration hasn’t called China out because, under emerging norms for espionage in cyberspace, information on Federal employees is considered a legitimate target.
Assuming the Chinese government was behind the incident, its cyber spies were doing exactly what they were trained to do. They were also doing exactly what we should expect them to do, and what we should be prepared to counter. As General Michael Hayden, former director of both the NSA and the CIA in the Bush Administration put it, “This isn’t shame on China. This is shame on us.”
When the Obama Administration has come out and publicly accused another country for a cyber attack, it hasn’t been for this kind of state-on-state spying. What the Obama Administration has strongly objected to is China’s campaign of economic espionage against American companies. In May of 2014, the Justice Department went as far as to hand down indictments for five Chinese military hackers, accusing them of carrying out a multi-year campaign to steal industrial secrets from U.S. companies for the purpose of sharing that information with Chinese companies.
Director of National Intelligence James Clapper has stated in clear terms that the United States intelligence community does not engage in this kind of spying. To do so would undermine the global marketplace by providing an unfair advantage to state-owned enterprises (of which the United States has none).
Getting China to stop this activity is at the top of our diplomatic agenda. Stopping foreign intelligence services from spying is not. If the Obama Administration had taken the advice of former Ambassador to the United Nations John Bolton, and kicked the Chinese Ambassador out of the country in response to the OPM attack, we would be setting a standard to which we would not wish to be held.
Even without the Snowden revelations, it is safe to assume that the denizens of Fort Meade have not yet all departed for Silicon Valley to work for venture-backed security startups. NSA’s mission is public and clear: to collect, process, and disseminate intelligence information.
Over time, we may decide that we need to impose limitations on cyber-spying. The Internet allows for espionage at a scale that was unimaginable during the Cold War. It also allows espionage to be carried out from the safety and comfort of a desk chair, without the personal risks famously taken by spies who operate in the real world. While Americans like Aldrich Ames and Robert Hanssen who sold secrets to the Soviets will spend the rest of their lives in prison, no such penalties can be imposed on the file servers that should not have shared their data with the Chinese. Without these natural limits, state-on-state espionage in cyberspace has few checks.
For now, the judgment of the national security community is that relative gains in intelligence are greater than relative losses. Simply put, we are better off in a world in which we can engage in this kind of spying, accepting that other countries will as well.
