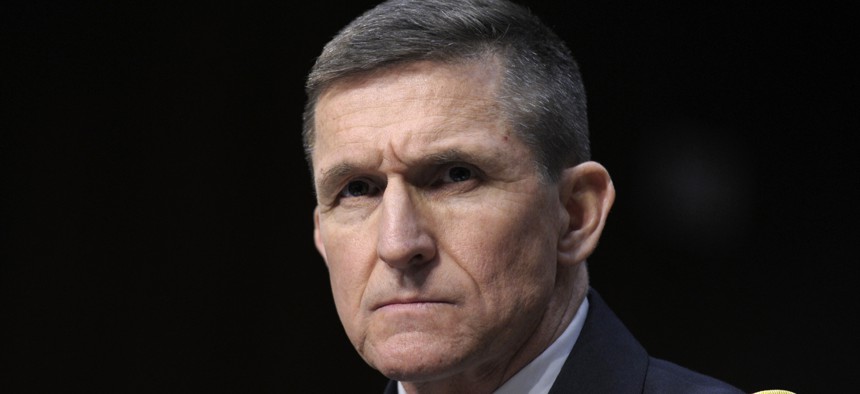
Defense Intelligence Agency Director Lt. Gen. Michael Flynn listens on Capitol Hill in Washington, Tuesday, March 12, 2013, during the Senate Intelligence Committee hearing on worldwide threats. AP / SUSAN WALSH
The Other Michael Flynn
Donald Trump’s national security advisor sounded very different when he was running counterinsurgency campaigns in Kabul.
Who is Michael Flynn, Donald Trump’s new national security advisor? There is no single or simple answer. The Flynn you’ve probably heard of, the one who hitched his wagon to Trump for-President, seems intent on convincing the world that he harbors a smoldering animus against Islam. He is a man whose worldview the American Conservative has described as “warped.” But there once was a Flynn who resembles the current man barely, if at all.
We can find this earlier Flynn in the papers he wrote while serving as an intelligence officer and in the relationships he formed with special operators working the tough fight in Afghanistan. Through these lenses emerges an innovator who sought to update intelligence collection and dissemination practices to comport with modern technology; an intelligence professional who emphasized building local ties with—yes—Muslim leaders to undermine the insurgent cause; and a manager who pushed hard for big changes, alienating entrenched power brokers in the intelligence community.
In 2010, Flynn was the director of intelligence for joint international forces in Afghanistan, working for top war commander Gen. Stanley McChrystal. Together, they reshaped how operators acquired information and intelligence to target enemies, emerging with a process sometimes called F3EAD, for Find, Fix, Finish, Exploit, Analyze, and Disseminate.
“They are the folks that ‘industrialized’ the targeting process of F3EAD,” said Stuart Bradin, a retired Army colonel who worked with Flynn in Afghanistan.
Flynn distilled the new ideas in a 2010 white paper, “Fixing Intelligence”, coauthored for the Center for New American Security, or CNAS. Its thrust: share more intelligence with and among more operators at the battalion and company level, and do it much faster.
“Currently, information this basic to a coordinating a successful counterinsurgency literally is inaccessible to the people who need it most. This failure not only jeopardizes an operation, but also exposes international efforts to ridicule for their ineptitude,” Flynn wrote.
In the paper, Flynn argued that the military should rely more on open-source data and much less on classified and expensive intel.
He also lamented the tendency “to overemphasize detailed information about the enemy at the expense of the political, economic, and cultural environment that supports it.” Read that mean intelligence operators were spending too much time on tactical data about specific targets and not enough time talking to Afghans, learning about real life among the people, who in what tribe or village had influence, what was the cost of basic necessities? The IC was missing the ground truth in the broadest possible sense. “Anti-insurgent efforts are, in fact, a secondary task when compared to gaining and exploiting knowledge about the localized contexts of operation and the distinctions between the Taliban and the rest of the Afghan population,” Flynn said, sounding very much like McCrystal himself.
The paper was widely read within and even beyond the military intelligence community. One serving intelligence analyst who has completed multiple assignments in Afghanistan told Defense One that “‘Fixing Intelligence’ was a formative paper for me as an intel officer. I've passed it along to pretty much all my peers.” He added “I guess there's a real discrepancy between LTG Flynn and LTG retired Flynn (much like we're probably going to see a difference between Candidate Trump and President Trump... hopefully).”
It was serving Flynn who showed a hunger for nuanced understanding in this 2010 interview about the vital importance of making friends at the tribal level.
“We really are reaching out to a much wider array of academia, via cultural experts, social experts, archeologists, anthropologists, people that frankly, traditionally, we wouldn’t reach out to. By bringing those subject matter experts in, we see the battlefield in a much different light,” he told NPR. “We’re trying to understand, what are the factors that the people of Afghanistan are willing to sacrifice their lives, time, talent and resources to achieve…. We don’t have as good a grasp of that as we should.”
When Flynn became director of the Defense Intelligence Agency in 2012, he placed a huge emphasis on open-source intelligence and rapid computational analysis to analyze it, something he discussed with Defense One at DIA headquarters in 2014.
“Just over a decade ago, when I was a senior intelligence officer, I spent most of my time in the world of ‘ints’ — signals intelligence imagery, human intelligence — and used just a little bit of open-source information to enrich the assessments that we made. Fast forward to 2014 and the explosion of the information environment in just the last few years alone. Open-source now is a place I spend most of my time. The open world of information provides us most of what we need and the ‘ints’ of old, they enrich the assessments that we’re able to make from open-source information,” he said.
One of the people that Flynn asked to help make sense of the new landscape of open-source intelligence was Ian McCulloh, a computer scientist at Johns Hopkins University. McCulloh, who worked with Flynn to trace foreign fighter networks in Iraq using large data sets, said the DIA director’s only mistake was trying to bring too much change too quickly.
“Intel was constructed in age of information scarcity. And we’re now in age of information superabundance. Flynn got that,” McCulloh said. “He wanted to leverage technology. He understood you had to have context from the lowest level up to the data scientist.”
This new greater emphasis on open-source data aided by computational analysis discomfited older, less technically astute intelligence professionals at DIA and in the broader intelligence community, McCulloh said.
“What that does is it largely disqualifies a lot of old intel guys in favor of people who have more technical skills. That was not happy for them. They wanted to wait him out. Screw him over,” he said. “Anybody who would say that he’s crazy or wrong, that’s an intel person who should be fired.”
More recently, a different Flynn has emerged, and the contrast to the first Flynn is significant and confusing. How could it be that someone who spent so much time emphasizing the importance of local network building, understanding the nuanced difference between life in Kandahar and Kabul, has since come to paint all of Islam as worthy of fear?
Fear of Muslims is RATIONAL: please forward this to others: the truth fears no questions... https://t.co/NLIfKFD9lU
— General Flynn (@GenFlynn) February 27, 2016
How could someone who “got” the operational value of big data not know that a search on a structured set of 690,000 emails could be done in a week?
IMPOSSIBLE:
— General Flynn (@GenFlynn) November 6, 2016
There R 691,200 seconds in 8 days. DIR Comey has thoroughly reviewed 650,000 emails in 8 days? An email / second? IMPOSSIBLE RT
If Flynn is innocent of both racism and ignorance, then how could someone so passionate about open source data collection be so very, very, very bad at Twitter?
Either way, Flynn will now have the power to remake much of the intelligence apparatus that he spent much of his career criticizing.
Time will tell which Michael Flynn shows up to do the job.
