sponsor content What's this?
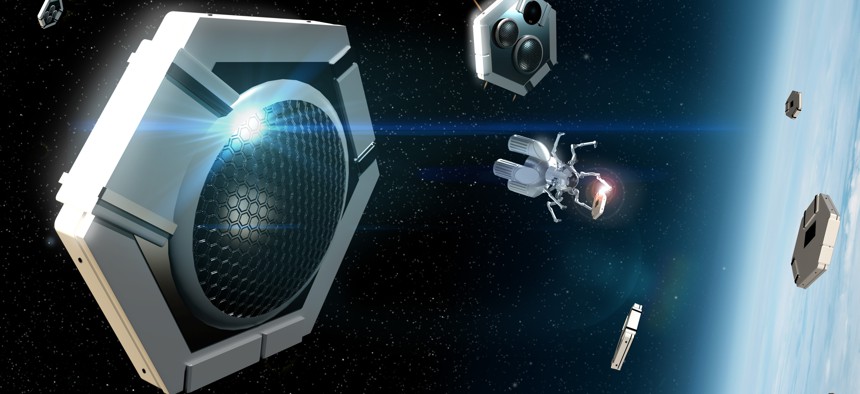
Rendering of future remote sensors in space Photo courtesy of Lockheed Martin.
The Future Will Rely on Autonomous Threat Detection for All Domains
From self-driving cars to fully automated factories, three decades from now the world is likely to be more connected than ever — which will also unlock a more sophisticated threat landscape. Autonomous threat detection will allow agencies to detect and respond to these ever-changing threats in real time.
Presented by
Lockheed Martin

The future is moving toward autonomous technology, requiring a new level of trust from humanity and improvements in connected communications to drive adoption and advancements. But operationally, these technologies will do much more: improve national cybersecurity offense, impact future space exploration, and ultimately, empower more sophisticated ways to protect and defend.
Consider the transportation industry. In 2050, autonomous vehicles will become more commonplace as capabilities improve. Humans will grow to trust and rely on autonomy as part of their daily lives, and transportation-as-a-service will be a norm. Rather than owning a car, imagine ordering a connected vehicle on an application similar to the ridesharing apps we know today that orders a car without a driver to pick up users and takes them from A to B.
The implications of this technology are even further reaching. Ideally, these vehicles won’t speed, break traffic laws or cause traffic backups. Law enforcement could reprioritize resources and overall safety could improve.
This is largely because the communication systems of these technologies would be globally connected. They would all be communicating with one another and have a sense of awareness of what other systems are doing by tapping into data from the cloud on demand.
James LeMieux, principal electro-optical engineer at Lockheed Martin, says this connectivity brings cyber defense to the forefront.
“In anticipation of this future new forms of autonomy and commerce that might exist, we're focusing on connecting everything together via a common infrastructure in the space layer and a multi-domain communications network where the connectivity is seamless,” he says.
In other words, the user won’t have to think about connecting from node to node, everything will be managed in the cloud.
“The joining of all of those nodes together into this infrastructure begins to emphasize the importance of cyber defense,” LeMieux adds.
Autonomous Security for an Autonomous World
As technology becomes more integral to our everyday lives and people become more dependent on network connectivity, it’s critical that those connections remain reliable.
“Cybersecurity becomes a crucial element to defending the network and ensuring that it’s up and reliable and can be trusted,” LeMieux says.
The same can be said for government agencies protecting their networks, especially in the face of an ever-evolving threat fabric. Cyber protection will be a huge consideration.
Dawn Beyer, a senior fellow with Lockheed Martin, says well-funded and persistent adversaries like nation-states use tactics and techniques that make the threat landscape more challenging, and require organizations to perform and respond in real-time.
“It'll be real-time attacks, real-time defense,” she says. “When reliance on that connected network is the norm, it will be even more important to protect. The ability to sense, rapidly reconfigure and respond to cyber threats and ensure uptime is critical.”
That criticality is amplified for advanced weapons systems. With more connected weapon systems, agencies must track these systems and maneuver very quickly, which LeMieux says presents a challenge with the current sensing architecture.
“In the future, you will not have the time to be able to sense and send data down to operators for them to make decisions,” he says. “The sensing layers need to be able to fuse that on the fly and pass information to the next sensor — and the next sensor — and so on. Being able to defend that cyber layer and communicate rapidly without ground intervention is incredibly important to keep custody of those physical threats.”
Another future threat to consider is anonymous adversaries launching missiles and other advanced threats while hiding their footprint, says Myland Pride, director of OPIR business development and strategy at Lockheed Martin.
Currently, technology can detect most threats based on different types of emissions. Imagine, however, how difficult defense against those threats would be if those emissions are less detectable.
“There'll be a need for artificial intelligence (AI) that can make decisions for us faster than we can make them today,” Pride says. “Ultimately, these systems will need to be able to detect, recognize intent, understand threat capability and communicate between sensors to address future sophisticated threats.”
That’s where autonomous threat detection comes in. Because of the need for more sophisticated, real-time detection techniques, autonomy must be baked into tomorrow’s sensing architectures.
Making Autonomous Threat Detection a Reality
Autonomy, in general, requires accurate models of the system — or system of systems — across all domains. For this reason, to make autonomy a reality for agencies, modeling, digital engineering and digital twins will be key. To meet these needs, Lockheed Martin is investing heavily in Model Based Systems Engineering (MBSE) and digital twins to facilitate the robust and accurate control required for autonomous systems to be trusted. Additionally, high resolution temporal and spatial sensors work in tandem with the system models to ensure control fidelity in the presence of system disturbances. Autonomous control algorithms must constantly make comparisons in a feedback loop between system models and the sensed environment in order to accurately determine control input.
Lockheed Martin is also building architectures that combine sensor inputs across many different systems, and all of these data must travel through an interconnected communications fabric. In space, this is referred to as the space data transport tapestry. Moving all of these data around requires higher bandwidth connections, and higher bandwidth connections require higher frequency carriers, which come with the challenge of smaller beamwidths. At long distances between highly dynamic nodes, such as those in space, pointing accuracy becomes incredibly important, but also incredibly challenging. There are tradeoffs between how much data can be processed at the edge to reduce bandwidth needs on the system subsequently alleviating physical layer challenges and what must be aggregated and fused centrally, and thus dependent on highly accurate interim connections from sensor to processing facility.
“If we have high-resolution sensors, but we don't have the bandwidth to transmit that data then the question becomes what kind of onboard processing do you need to reduce that data down, and then share that information in a compressed way to deal with bandwidth bottlenecks?” LeMieux asks.
The combination of sophisticated, high-fidelity models of all the physical network layers, high-fidelity sensors and edge processing is a critical investment in enabling the autonomy of the future. Additionally, and as a necessary complement, industry must develop in parallel seamless and secure connectivity between terrestrial and space-based sensors to ensure robust and trusted autonomous systems have the local and global reference data needed to carry out their missions automatically.
And as a holistic initiative, government and industry must work together to conduct physical demonstrations in orbit or on platforms for high-bandwidth optical communications capabilities, as well. Combined, this will help make a cross-domain multilayered sensor architecture a reality.
Lockheed Martin Lays the Groundwork for Next-Level Cybersecurity
As Lockheed Martin prepares for this 2050 timeframe, it’s also exploring a network for multi-domain assets so devices in each domain can seamlessly connect and share data — think 5G or 6G technologies, which bring more reliable, higher throughput and lower latency connectivity to autonomous systems, working in tandem with other communication layers in various domains.
Lockheed Martin’s 5G.MIL® Solutions offer a key way to provide the communications necessary for a Joint All-Domain Operations (JADO) approach. The system integrates military communications and enhanced 5G technology to enable connectivity and data flow across assets.
This communications architecture is a big part of a 2050 autonomous future. Lockheed Martin is invested in figuring out ways to manage these future ubiquitous communication capabilities so devices in various domains with different network nodes can communicate in an orchestrated fashion.
Advancing technologies like these requires hardened protections. Organizations will have to ensure their data’s confidentiality, integrity and availability, by trusting their platform is resilient.
The company is also building AI systems to provide more accurate, rapid and predictive data-driven approaches for more rapid classification and identification of objects, anomaly detection and automatic target recognition.
“They have to be able to rapidly detect any type of anomalies on that platform or that system,” Beyer says. “It goes back to where humans are just not fast enough to do that.”
And it takes Lockheed Martin back to cyber defense. Its continued investment and research into full spectrum cybersecurity capabilities builds the platforms, tradecraft and tools to help move faster, be safer and improve quality.
As technology evolves, as does the capability of adversaries -- and the communications architecture and networks of the future rely on stronger cyber defense. Data trust and network resilience will be key.
“There's always more than just evolving the technology,” Beyer says.
Check out how Lockheed Martin is making this vision of 2050 a reality.
This content is made possible by our sponsor. The editorial staff was not involved in its preparation.
NEXT STORY: Why Self-propagating Robots Are the Future of Space