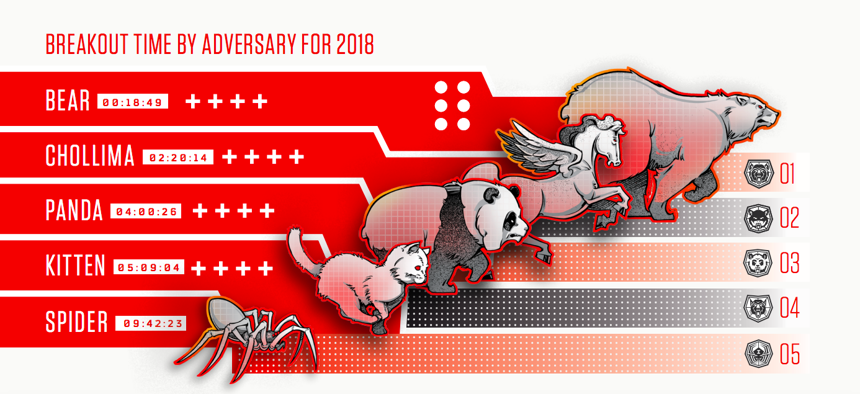
A graph showing the relative breakout time of state-sponsored (and independent) cyber threat groups. Crowdstrike
You Have 19 Minutes to React If the Russians Hack Your Network
After Moscow's hackers breach one PC, that network's defenders have less than a half-hour to prevent wider data theft or destruction, a new report finds.
Nineteen minutes. That’s how long the average victim of a Russian state-sponsored hacking group has to react before the initial penetration of a network becomes wider access, theft, and destruction, according to data published today by computer security company CrowdStrike.
By comparison, the second-fastest groups were North Koreans, who needed an average of two hours to jump from the first compromised computer to the second; Chinese groups needed an average of four hours.
Dubbed “breakout time,” the statistic refers to the amount of time it takes the attacker to jump between network nodes once on the network. It also “shows how much time defenders have on average to detect an initial intrusion, investigate it and eject the attacker from the network, before sensitive data can be stolen or destroyed,” CrowdStrike analysts wrote in a 2018 post introducing the concept.
The agility of Russian groups has long been known; it was a signature element of both the 2015 penetration of the Joint Chiefs’ civilian email system and the following year’s attack on the Democratic National Committee’s network. But the new data is eye-opening.
“The stats are likely driven by a cross of several factors: the skills and capability of each; the relative risk calculus each is making in their likelihood of getting caught and the consequences; to whether they are just exploring for targets that present themselves or going into a predetermined target with something very specific in mind. But an average of 18 minutes is really quite amazing given the scale. Game respects game,” said Peter Singer, a senior fellow at New America and author, most recently, of LikeWar: The Weaponization of Social Media.
The CrowdStrike report also notes that Chinese activity has been increasing against the United States, reiterating earlier findings by government and industry analysts.
But the threat posed by Russia remains key in the minds of lawmakers and intelligence professionals. During a recent Senate Armed Services Committee hearing, Sen. Richard Blumenthal, D-Conn., hinted at certain classified “successes” by U.S. Cyber Command against Russian hackers in 2018.
“The threat from Russia remains unabated. Can you say that in public?” asked Blumenthal of Gen. Paul Nakasone, the head of U.S. Cyber Command and the NSA.
Nakasone responded, “Russia provides a sophisticated threat to our nation.”
In 2018, the Russians targeted defense and military entities throughout Europe and NATO as well as think tanks, the PyeongChang Winter Olympic Games, and even the Swiss lab working the Skirpal poisoning case.
While Russian election disruption didn’t really happen in 2018, it remains a threat. Chris Krebs, DHS Cybersecurity and Infrastructure Security Agency Director, told reporters last week, “We are doubling down [on election security] in advance of the 2020 election...Despite what some of the reporting might be, election security and countering foreign influence efforts aren’t going anywhere.”
The CrowdStrike data further cements Russian cyber operators’ reputation as aggressive and effective, echoing earlier analysis
In a 2017 paper, researchers from Arizona State University revealed that a propensity to exploit a particular known vulnerability depended greatly on whether the attackers were Chinese, Russian, or American, etc. The researchers looked at Dark Web chatrooms where hackers were actively discussing recently disclosed vulnerabilities to hit the National Vulnerabilities Database. If the hackers discussing the bug were Chinese, the chances of someone trying to exploit the vulnerability in question was nine percent. But if the conversation was in Russian, the probability of hacker attempting to exploit the flaw was 40 percent.
“The Russians are the most aggressive and risk-tolerant because they’ve broken so many international norms and faced so few repercussions that they don’t really believe there will be any serious consequences to their action,” said Mike Carpenter, a former deputy assistant defense secretary for Russia, Ukraine, and Eurasia who now helps lead the Biden Center for Diplomacy and Global Engagement at the University of Pennsylvania. “That’s partly why the Russians are so comfortable going beyond network intrusion and actually manipulating data or taking down power systems, as they’ve done in Ukraine.”
