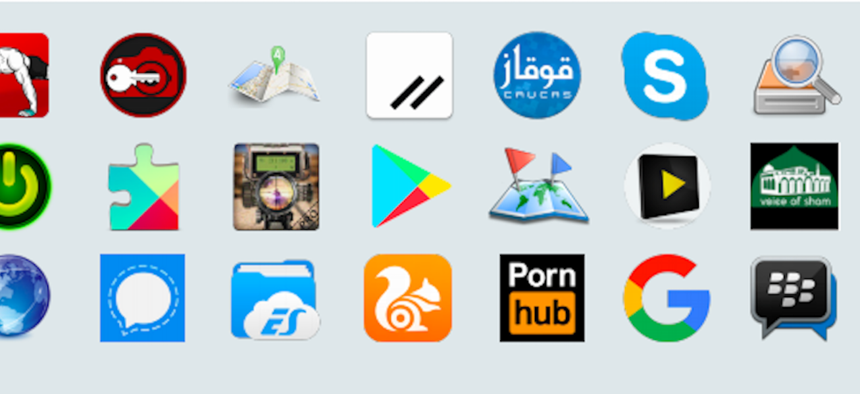
A graphic from a report from Lookout, published on Wednesday, July 25, 2019, showing "trojanized" versions of popular apps made to carry malware. Lookout
Russian Hackers Build Fake Skype, Signal, Pornhub Apps to Lure Victims
Installing the apps activates malware that steals personal data and sends it off to St. Petersburg.
Be careful what apps you download, especially if you are in the Caucasus. Someone is packaging powerful malware in fake versions of popular Android applications such as Skype, Signal, and PornHub, according to a report released Wednesday by the Lookout cybersecurity firm.
Dubbed Monokle, the malware can “exfiltrate data from third party applications by reading text displayed on a device’s screen at any point in time,” the report said.
Monokle seeks root access, the most privileged level of control. When it achieves that access its able to overwrite security certificates to intercept--and potentially change-- incoming and outgoing information, sometimes called a man-in-the-middle attack. But it can operate and steal data even when it can’t access root (because of systtem configuration.) “This allows the software to be incredibly flexible and useful in multiple operational scenarios,” they note.
The researchers first spotted Monokle in 2016, and have seen it pop up in the wild. But they’ve also seen it as part of highly targeted campaigns, one aimed at Muslim men in the Caucasus region and another at people interested in Syria’s Ahrar al-Sham group, one of the Islamic militant groups fighting the Assad regime. These efforts peaked in 2018, simultaneous with heavy Russian military action against anti-Assad groups.
Lookout determined that Monokle was developed by the Russian Special Technology Center, a group linked to the GRU, Russia’s military intelligence agency. The group was sanctioned by the U.S. government for its role in the 2016 attack on the U.S. presidential election. The evidence? Some of the developers known to work for the STC literally signed their work.
“While conducting this investigation, Lookout researchers came across a number of potential developer names that appear to be linked to Monokle or software connected to STC. Some of these leads provided Lookout with the evidence to link development operations within STC to IOCs [indicators of compromise] associated with Monokle,” they write.
Lookout reports that the STC is hiding the malware in fake “trojanized” versions of many popular apps, and some less popular ones to appeal to specific target groups.
“The Monokle surveillanceware capabilities have appeared in trojanized applications — that is, applications that contain the legitimate functionality (of Skype, Signal and PornHub) and look and feel exactly like the legitimate apps, but are not legitimate and are infected with Monokle malicious functionality,” said Apurva Kumar, a staff security intelligence engineer at Lookout. “This is a common technique that malware developers use. They ‘re-package’ a well-known application with malicious functionality so as not to arouse user suspicion.”
Lookout highlights more than 80 indicators of compromise to help people determine if the malware is on their phone.
And they say STC’s help-wanted listings suggest that the group is working on a version of the malware for Apple phones as well.
Related podcast:
