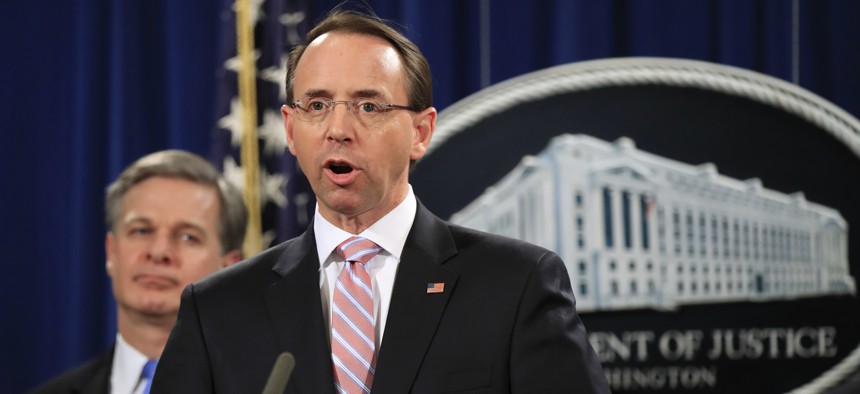
Deputy Attorney General Rod Rosenstein with FBI Director Christopher Wray, speaks during a news conference at the Department of Justice in Washington, Thursday, Dec. 20, 2018. AP Photo/Manuel Balce Ceneta
DOJ Hits Chinese Hackers For Attacking U.S. Navy, Agencies, Companies
Hackers with the Chinese government hit 45 targets in campaign going back years.
Two Chinese nationals conducted a massive, multi-year effort to steal information from U.S. companies, government outfits — even Navy personnel according to the Department of Justice, working with the United Kingdom. The new indictments, released by DOJ offcials Thursday, are the latest sign that Chinese cyber espionage activity is on the rise three years after a historic deal between then-U.S. President Barack Obama and Chinese President Xi Jinping to curb such activity between the two countries.
The indictments name Zhu Hua and Zhang Shilong of the group APT10, or “Stone Panda,” as conspirators in a plot to attack managed cloud service providers and steal valuable info from 45 entities, including technology companies, the U.S. Department of Energy, and NASA. In addition, it claims that the hackers obtained highly sensitive personal information from members of the military, including social security numbers, email addresses and salary information on 100,000 U.S. Navy personnel. The Navy declined to comment on the indictments, referring reporters to the Justice Department.
The APT10 hacking efforts go back to 2014, DOJ officials said. But intelligence officials have for months said that China hasn’t been living up to its 2015 promises. In July, officials with the National Counterintelligence and Security Center issued an unclassified version of a report that described growing Chinese cyber espionage activity.
Related: Russia Is the Biggest Backer of Cybercrime. The US Must Get Serious About Deterrence
Related: Inspectors Find Big Cyber Vulnerabilities in US Missile Defense System
Related: China is Exporting its Cyber Surveillance to African Countries
The Department of Homeland Security and the State Department issued a rare joint statement on Thursday.
“The United States is concerned that this activity violates the 2015 U.S.-China cyber commitments made by President Xi Jinping to refrain from conducting or knowingly supporting ‘cyber-enabled theft of intellectual property, including trade secrets or other confidential business information, with the intent of providing competitive advantages to companies or commercial sectors,’” according to the joint statement.
The State Department earlier attributed the Marriott hack revealed earlier this month, exposing personal information on as many as 500,000 people, to China.
The indictments follow reporting from the Wall Street Journal last week that revealed that Chinese hackers had penetrated the networks of Navy contractors to steal valuable information, a hacking effort that began 18 months ago. The breach has prompted a “top-to-bottom” review of cyber vulnerabilities and security processes, Navy officials said.
Private cybersecurity companies have likewise observed an uptick in cyber-espionage activity from China. “For the past year, CrowdStrike has been reporting on the increase of activity we’ve seen from Chinese state-affiliated cyber threat actors, aimed at stealing trade secrets from nearly every sector of the economy, including biotech, defense, mining, pharmaceutical, professional services, transportation, and more,” Crowdstrike co-founder and Chief Technical Officer Dmitri Alperovitch said in a statement on Thursday. Crowdstrike maintains that Stone Panda is affiliated with China’s Ministry of State Security, which Alperovitch called “he most active Chinese cyber threat actor.”
Ben Read, a senior manager of cyber espionage analysis at cybersecurity company FireEye, said, “APT10 has been tracked by FireEye for years and is one of the most prolific cyber espionage groups..their move towards compromising managed service providers (MSPs) showcases the danger of supply chain compromises and reflects their continuously evolving tactics. APT10 is a well-resourced and a global threat.”
The combined U.S. and U.K. effort evinced growing international impatience with recent Chinese activity, according to Priscilla Moriuchi, director of strategic threat development at Recorded Future. “The international consensus seems to be building to confront China over what the West views as unfair and illegal business practices,” she said. “The US government continues to take the theft of personally identifiable information (PII) of US citizens very seriously. The FBI emphasized the theft of PII from 100,000 US service members. This is especially timely, as Secretary of State Pompeo has attributed the SPG/Marriott PII theft to China” to Moriuchi.
