Number of Security Clearance Holders Drops 12 Percent
Federal agencies have trimmed the ranks of employees and contractors with access to classified information.
The number of individuals holding government-issued security clearances at the end of fiscal 2014 was 12 percent lower than the previous year, according to a new report, marking a successful effort by federal agencies to cut the number of employees and contractors with access to classified information.
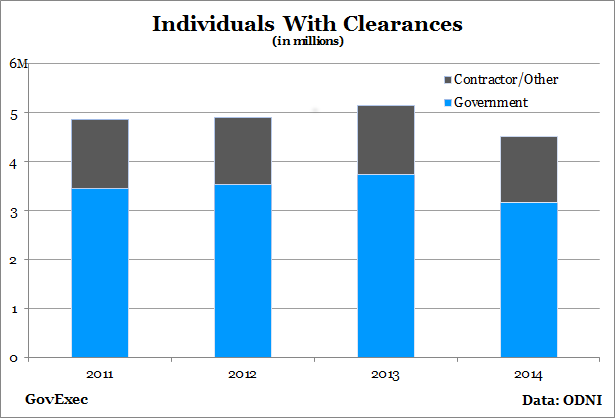
The Office of the Director of National Intelligence report showed a dramatic turn in the trend of a growing security cleared population. The number of people with clearances has ticked up each year since ODNI began measuring it in 2011. The number of newly approved security clearances continued the downward trajectory it has been following for several years.
About 4.5 million people held security clearances at the end of fiscal 2014, compared to 5.1 million at the close of fiscal 2013. The cleared population was the smallest since 2010, the first year the statistics were available. The number of newly approved background checks -- including both first-time issuances as well as reinvestigations -- dropped 14 percent to 665,000.
“These decreases were the result of efforts across the [U.S. government] to review and validate whether an employee or contractor still requires access to classified information,” ODNI wrote, “and several additional Department of Defense initiatives to review its cleared population.”
The Obama administration set a goal to reduce the number of cleared individuals by 10 percent by 2018 compared to five years prior. The Defense Department has issued several directives to identify employees who no longer require clearances and strip them of the status.
Steven Aftergood, director of the Federation of American Scientists Project on Government Secrecy, said the clearance cuts were a positive development that showed the system was not a “runaway train.”
“My impression since 2010 was the system was drifting,” Aftergood told Government Executive. “Each year more clearances were added on. It’s striking to see in the past year there was a very deliberate reduction.”
In the two years since former National Security Agency contractor Edward Snowden leaked hundreds of thousands of classified documents to the press and contractor Aaron Alexis fatally shot 12 people at the Washington Navy Yard, the White House and lawmakers have proposed myriad changes to the security clearance process. Reform efforts have focused on reducing the amount of classified information -- thereby reducing the size of the cleared population -- as well as boosting reinvestigation efforts.
Still, losing a clearance after initial approval is rare. The National Geospatial-Intelligence Agency rejected recertification the most of any intelligence agency, according to the report, taking away just 2.2 percent of clearances. NSA maintained the highest rejection rate for new applicants, turning down 9.2 percent. The agency approved 99.9 percent of its reinvestigation cases.
ODNI said in its report that as it and other agencies refocus on ensuring those with clearances actually need and deserve them, the timetable for approving new cases could lengthen. Agencies have for years pushed -- with significant success -- to lower the time involved in receiving a clearance.
The fastest 90 percent of investigations for secret clearances took an average of 46 days as of April 2014, while top secret took 109 days. The same category of investigations in aggregate took 265 days in 2005.
Aftergood said continuing to declassify information will lead to further reductions in clearances granted, which in turn will save money and create better investigations.
“There’s still some fat in the system that could be trimmed away,” he said. “The experience in the last year has shown that that’s possible.”




