Pentagon Running Low on Smart Bombs for ISIS Campaign
In a preview of the Pentagon’s 2017 budget, Defense Secretary Carter signals a coming acceleration of the 18-month-old bombing effort.
The Pentagon is starting to run low on the smart bombs and guided missiles it has used in the 9,000-plus airstrikes against Islamic State militants in Iraq and Syria over the past 18 months, U.S. Defense Secretary Ash Carter said Tuesday.
Because of that, President Barack Obama will ask Congress next week to approve $1.8 billion to buy 45,000 new bombs. The spending request is part of $7.5 billion the Pentagon says it will need to bomb ISIS and train Iraqi security forces in 2017.
“This will be critical as our updated coalition military campaign plan takes hold,” Carter said of the request for the Pentagon’s war chest.
The secretary, in a speech to the Economic Club of Washington, outlined major themes within the Pentagon 2017 spending plan, which the Obama administration will send to Congress next week.
Carter said the Pentagon is at “a major inflection point” and that its $583 billion 2017 budget takes “the long view.”
He also announced a host of new technological projects to address near-term and strategic threats. Among them is the “arsenal plane, which takes one of our oldest aircraft platforms, and turns it into a flying launch pad for all sorts of different conventional payloads.”
While he did not specify the platform, it is likely the B-52 bomber, which has undergone a multitude of upgrades since it first flew in the 1950s.
“In practice, the arsenal plane will function as a very large airborne magazine, networked to 5th-generation aircraft that act as forward sensor and targeting nodes – essentially combining different systems already in our inventory to create wholly new capabilities,” Carter said.
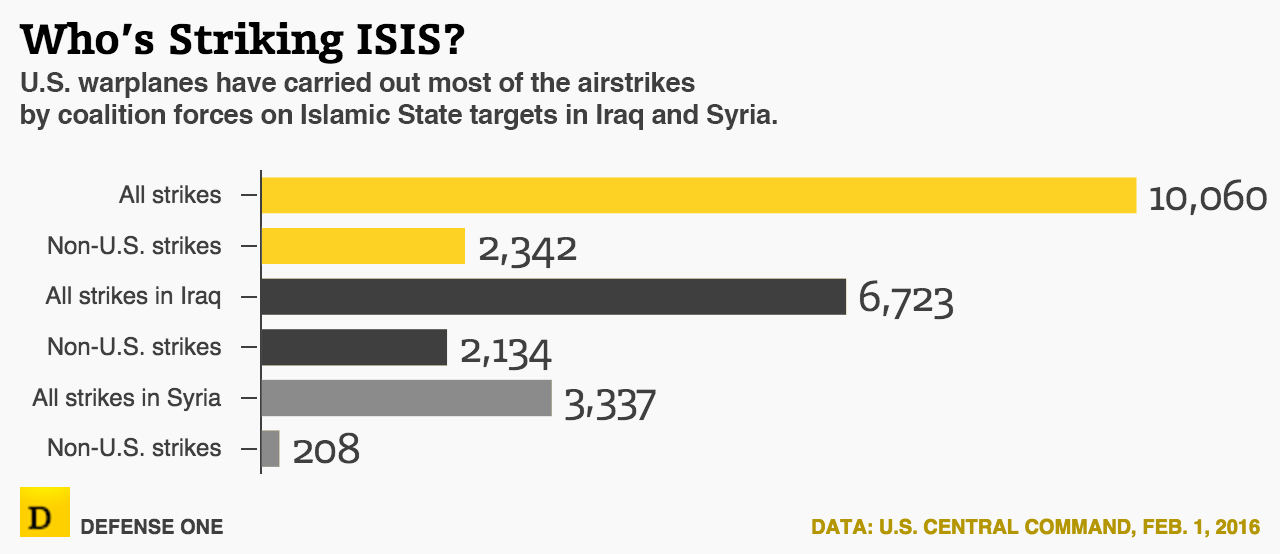
Since August 2014, the Pentagon has conducted more than 9,000 airstrikes against ISIS. As of Dec. 31, the Pentagon used $1.3 billion worth of bombs and missiles. Those airstrikes have destroyed more than 20,000 ISIS targets.
The bombing campaign against ISIS is costing about $11.2 million per day, Air Force Times reported earlier this month.
The increase in the Pentagon’s war budget signals that the U.S. military’s campaign against ISIS will accelerate over the next two years.
Still, the ISIS money is only a fraction of the Pentagon’s war chest. For the current fiscal year, Congress approved $59 billion, $8 billion more than the Pentagon requested, for the 9,800 troops that remain in Afghanistan and continue the airstrike against ISIS in Iraq and Syria.
The war budget, formally called the Overseas Contingency Operations (OCO) account , is the conduit for unexpected expenses in the military’s fights overseas and related training stateside. But critics say it is too often used as a way to get around Pentagon spending caps.
Lt. Gen. John “Mick” Nicholson, President Barack Obama’s pick to lead American forces in Afghanistan, told senators last week during his confirmation hearing that he would review the planned troop drawdown in the country. U.S. forces are supposed to leave Afghanistan by the end of 2017, but a resurgence in Taliban attacks has put that in question.
“[W]e’re in this for the long run,” Carter said of Afghanistan at a briefing last week. “The president has made a commitment, and all the coalition members have to stick with Afghanistan. That's not just for the year 2016. It's the year 2017 and beyond.”
Carter said last week that the Pentagon’s 2017 war budget would include funding, as it has in the past, for Afghan security forces. He also said would make “contributions” as well.
Lawmakers have tried to use the war budget to skirt Pentagon spending caps, but the Obama administration has rejected those attempts .
The budget deal struck by Congress for this year and next stipulated the Pentagon will get at least $59 billion in 2017, but that account is not capped and they could get more.
“At this point, trying to project OCO costs is complicated because OCO includes so much more than war-related costs for Iraq and Afghanistan,” said Todd Harrison, a budget analyst with the Center for Strategic and International Studies. “OCO has become a semi-permanent addition to the base budget, effectively a catch-all for priorities that don't fit within the ... budget caps. The level of OCO funding has become more of a political calculation than a budgetary calculation.”




