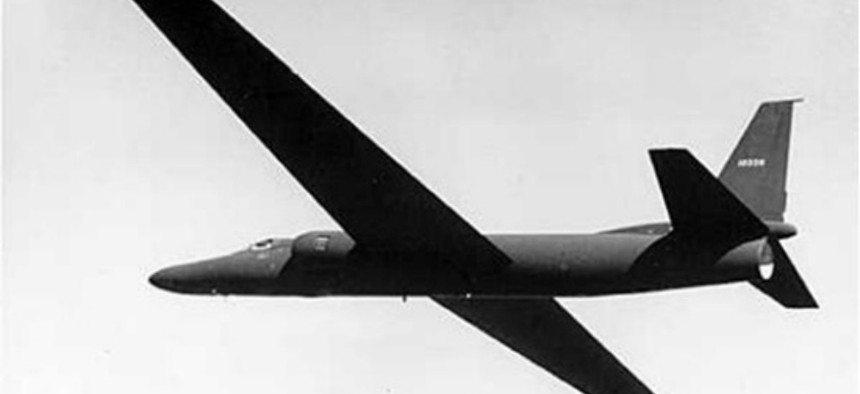
Early U-2 in flight. Central Intelligence Agency
Area 51 Has Been Hiding U-2 Spy Planes, Not UFOs
The existence of Area 51 isn’t the CIA’s most impressive revelation within the newly declassified document—it’s the U-2’s price tag. By Mark Micheli
Add confounding thousands of conspiracy theorists -- and inspiring six decades of science fiction -- to the U-2 spy plane’s already impressive resume. A newly declassified CIA history of the aircraft reveals that Area 51 does, indeed, exist and that the air base wasn’t built to hide evidence of a secret alien crash landing—but specifically for testing Lockheed’s U-2 spy plane.
If you don’t know the U-2 then you don’t know the U.S. military. It’s just about the only piece of military technology that hasn’t changed in the last 60 years. With the completion of its first successful mission over the Soviet Union in 1956, the U-2 has been the aerial reconnaissance mainstay of the Air Force for 58 years (beating out, as recently as last year, Northrop Grumman’s Global Hawk UAV as the Air Force’s surveillance aircraft of choice). Originally designed to fly out of range of enemy missiles and fighters, the U-2 can literally fly to the edge of space -- reaching heights of 70,000 feet, where it’s often as high above commercial airliners as those airliners are above the ground.
And, according to the CIA document, it’s for exactly that reason that there was a sudden surge in mid-1950s UFO sightings near a top secret military base north of Indian Springs, Nevada (aka Area 51):
“In the mid-1950s, most commercial airliners flew at altitudes between 10,000 and 20,000 feet and military aircraft like the B-47s and B-57s operated at altitudes below 40,000 feet. Consequently, once U-2s started flying at altitudes above 60,000 feet, air-traffic controllers began receiving increasing numbers of UFO reports.”
According to the CIA report, in the evenings the U-2’s silver wings would catch and reflect the setting sun’s light and, flying at 60,000 feet, appear as “fiery” objects to airline pilots flying at 20,000 feet. By checking flight records, the Air Force found that “U-2 and later OXCART flights accounted for more than one-half of all UFO reports during the late 1950s and most of the 1960s.”
But, you know, the truth is out there and this explanation isn’t likely to satisfy the tinfoil hat crew. But the existence of Area 51 isn’t the CIA’s most impressive revelation within the declassified document—it’s the U-2’s price tag.
The CIA originally contracted Lockheed to build 20 U-2 at $22.5 million. But, in a turn of events unheard of in modern defense contracting, Lockheed built all 20 aircraft under budget for a total of $19 million, at less than $1 million per aircraft.
Read the CIA’s complete declassified documents at The George Washington University’s National Security Archives.
