U.S Air Force/AP
A Look at the U.S. Nuclear Arsenal, From 1945 to Now
Air Force officials say the country's nuclear arsenal is safe despite recent reports of crime and corruption. But what does it actually look like? By Matt Vasilogambros.
When it comes to America's nuclear arsenal, any error could be catastrophic.
That's why news of corruption and crime coming out of the U.S. Air Force this week was so alarming. On Wednesday, the Air Force said that 34 officers responsible for launching this country's nuclear missiles were suspended because they were cheating on their monthly proficiency tests on how to operate the warheads.
Additionally, other Air Force officers in charge of nuclear codes are involved in an investigation involving illegal drugs.
Air Force officials say the country's nuclear arsenal is safe. But what does it actually look like?
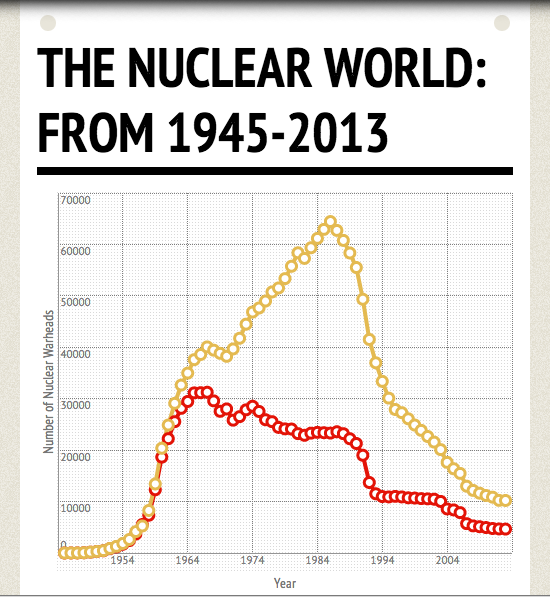
Using statistics from a Bulletin of the Atomic Scientists study from September, here is a look at nuclear weapons since 1945. The number of nuclear weapons stopped its steady incline in 1986 after the U.S. and Soviet Union agreed to two nuclear arms reduction treaties.
(Click below to see the full infographic)