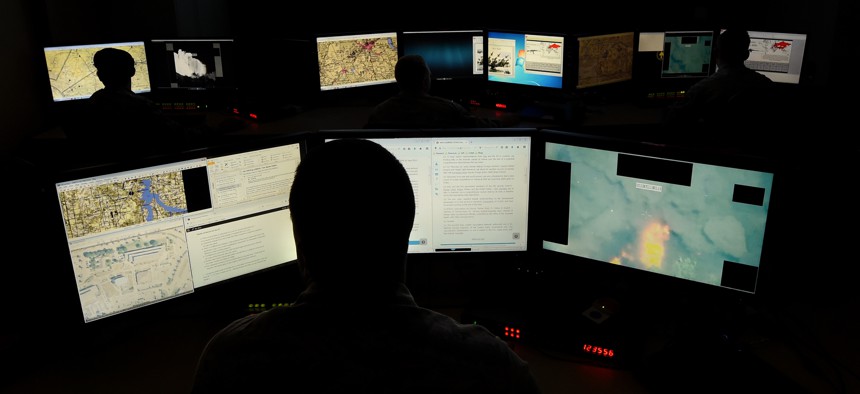
Airman Kai White/U.S. Air Force
The Pentagon’s Bug Bounty Program Should Be Expanded to Bases, DOD Official Says
The ‘best and brightest’ hackers could accelerate the search for vulnerabilities across some of the Defense Department’s broader critical infrastructure.
The Hack the Pentagon bug bounty program that allowed citizens to test the defenses of Defense Department websites could soon see a spinoff inviting hackers to probe the Pentagon’s critical infrastructure.
Building and electrical systems, HVAC equipment and other critical infrastructure laden with internet-connected sensors often run on operating systems unsupported by vendors. Even as the Pentagon pushes to upgrade its information systems to Windows 10 by this year, its critical infrastructure remains woefully behind.
“About 75 percent of the devices that are control systems are on Windows XP or other nonsupported operating systems,” said Daryl Haegley, program manager for the Office of the Assistant Secretary of Defense for Energy, Installations and Environment.
Haegley, speaking Thursday at an event hosted by OSIsoft, said the assessment was based on visits to 15 military sites. Microsoft stopped providing support for Windows XP in 2014. Haegley, however, said some of the systems that run DOD facilities are far older.
“A lot of these systems are still Windows 95 or 98, and that’s OK—if they’re not connected to the internet,” Haegley added.
Increasingly, though, sensors in these kinds of systems do connect to the internet, or at least newer components of them do. Famously, the Target data breach wasn’t a hack of Target itself, but rather information stolen from an HVAC vendor that worked at its stores. Often, there’s not one person in charge of ensuring these systems are protected, Haegley said.
While DOD is reacting to the threat—a November memo assigns some security responsibilities to DOD’s critical infrastructure—Haegley said he’d like to see a Hack the Pentagon for its critical infrastructure. DOD’s bug bounty program revealed 138 previously undisclosed vulnerabilities and cost about $150,000.
Haegley said he’s seeking senior staff buy-in on the idea. In such an effort, vulnerabilities at one building site would likely help DOD shore up facilities elsewhere.
“The best and brightest could help us get through that,” Haegley said.
