
The Shenyang J-31 (F60) Photo via airliners.net by wc
China's Copycat Jet Raises Questions About F-35
Did the Chinese theft of data on the US fighter jet and other weapons shrink the Pentagon's technical superiority?
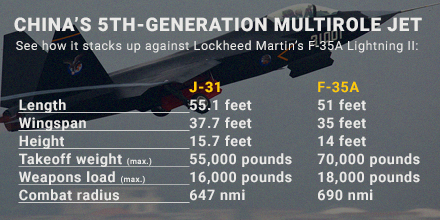
New technical specs about China’s new J-31 fighter, a plane designed to rival the American-made F-35 Joint Strike Fighter, popped up on a Chinese blog last week. So who has the advantage — the U.S. or China?
China’s twin-engine design bears a striking resemblance to the single-jet F-35. Still, the Joint Strike Fighter is expected to fly slightly farther and carry a heavier load of weapons, according to the data, which was first reported by Jane’s.
Military experts say that while the J-31 looks like, and may even fly like, the F-35, it’s what’s under the hood and embedded in the skin that really matters. The U.S. has the better computer software, unique sensors and other hardware, stealth coating, and engines technology—all critical attributes that make fifth-generation aircraft different than the military jets of last century.
Exactly how long that advantage lasts is up for debate; senior Pentagon officials and experts believe American technology superiority is shrinking. That means the U.S. military’s weapons will not overmatch adversaries for as long as they have in past decades.
“It’s basically, are they producing weapon systems that have fifth-generation characteristics that potentially nullify some of our planned advantages in the future battlespace,” said Peter Singer, a strategist and senior fellow at New America.
“[W]e were depending more so on the [American weapons] having that generation-ahead edge, and if we don’t have that generation-ahead edge, that is incredibly scary for us in various scenarios,” Singer said.
U.S. Deputy Defense Secretary Robert Work and acquisition chief Frank Kendall have spent much of the past two years warning that the U.S. military’s technology advantage is eroding.
“What it does is reduce the cost and lead time of our adversaries to doing their own designs, so it gives away a substantial advantage,” Kendall said of cyber espionage at a 2013 Senate Appropriations Defense Subcommittee hearing.
Since then, Work and Kendall have been leading projects to find technologies that will give the American military an advantage on the battlefield of the future.
China is suspected of stealing F-35 design data in 2009. U.S. officials have said classified information was not stolen in that breach, but in 2011 it emerged that China was building a multirole, stealth fighter of its own that could strike targets in the air and on the ground, like the F-35. The J-31 flew for the first time in 2012.
The Pentagon huddled with defense companies in 2007 to urge firms to better protect their networks. Companies are attempting to beef up their cybersecurity, but there is a gap in the security talent, said Justin Harvey, chief security officer for Fidelis Cybersecurity, a firm that works with the U.S. government and private industry.
“They’re buying these tools, but they’re not investing a ton in the people,” he said. Whenever a company is attacked, they typically call Fidelis or similar cybersecurity firms to consult because they don’t have employees with the training or experience to assess the breach.
“I think 90 percent of U.S. companies are not equipped to deal with cyber espionage,” Harvey said.
The defense industrial base and financial services industry are the best-protected, he said.
Cyber espionage allows rival companies to get access to the information gleaned during testing “for the cost of breaching your network,” Singer said.
Cyber theft allows China to save tens of billions of dollars in research-and-development, the experimentation and testing a new weapon goes through before it reaches the battlefield, experts say. While the Chinese jet fighters might still be inferior to the American planes, not having to do early research and development allows them to focus on upgrades and improvements.
This means the 10- to 20-year advantage an aircraft like the F-35 was supposed have on the battlefield might not be there, Singer said. Those Chinese plans could then compete against U.S.-made aircraft 20 years from now when the U.S. government allows more and more allies to buy the F-35.
“Those future competitions will be incredibly difficult because we’ll have paid the R&D for our competitors,” Singer said.
Increased research-and-development costs, ever common in Pentagon acquisition projects, often lead to a decrease in the total number of items purchased. Most recently, this was the case with the F-35’s older brother, the F-22 Raptor. The Air Force had wanted more than 700 planes, a number cut first to 381 and ultimately to 187.
“The expense of our fifth-generation [fighter aircraft] means we have not been able to buy as many as we want,” Singer said.
But the F-35, unlike previous aircraft, has been designed to receive upgrades over the years, which will ultimately improve its capabilities, allowing it defeat new threats.
F-35 development will end in October 2017. After that the program will move into a “follow-on development” phase, said F-35 project spokesman Joe DellaVedova. “One of the F-35’s great strengths is that it’s a growth platform, so its software, its processors, its radar, its capability; there’s a lot of room for growth."
The jet fighters will get software and hardware upgrades every two years on an alternating basis.
The F-35 itself and its ground equipment undergo multiple tests each year to make sure the systems can withstand cyber attack, DellaVedova said. “We take the cyber threat very seriously,” he said.
While the Chinese planes might still have inferior systems, stealing intellectual property and subsequent R&D savings also allows Beijing to make drastic changes in prototypes.
For the J-20, a Chinese stealth fighter being built to rival the F-22, there have been numerous prototypes in which the plane’s design has become stealthier, Singer said.
“Their designs, their capabilities are shifting from prototype to prototype in a way that has not happening with the current way that we are building our fifth-gen systems,” he said.





