New hacking scenario emerges: Wi-Fi signal-sniffing drones
Security analysts are increasingly concerned about camera-carrying drones that could also be used to breach wireless networks.
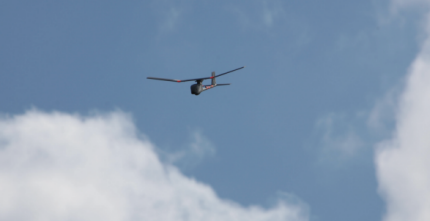
The next major network security threat could come from the sky, in the form of drones equipped with video cameras and the ability to sniff out mobile devices and their unique identifiers, perhaps even establishing rogue network access points in the sky that could be used to hack sensitive government or corporate networks.
That's the potential threat, according to security specialists and at least one network security company offering detection equipment to address the new threat from the sky posed by network-hacking drones.
The inherent openness of Wi-Fi and other wireless networks, along with the proliferation of mobiles devices constantly seeking network connections, provide a tempting target for signal-sniffing drones. Experts stressed that the security perimeter of an office building will now have to include the airspace around the structure, because that airspace can be easily surveyed by drones at standoff distances capable of relaying video about, say, an agency's wireless infrastructure.
In another scenario, security analyst Glenn Wilkinson described how he rigged a "distributed, tracking, profiling and data-interception framework" called "Snoopy" to a quadcopter drone.
"I can get to altitude, I can fly this device at [an altitude of] about 80 meters. You won't see it, you won't hear it, but with the right antenna I'll be able to detect [device] signals from the ground," Wilkinson told the Black Hat Asia hacker conference earlier this year.
Consumer drones are readily available and relatively inexpensive—something that has not been lost on the military services, which have stepped up their search for anti-drone technologies and increased their focus on electronic warfare. Countering an adversary’s surveillance or attack capabilities has been the major focus, but airborne cyberattacks could also come into play. Not only do bases at home and abroad have wireless networks, but wireless forms the backbone of tactical battlefield communications.
Domestically, regulators at the Federal Aviation Administration are scrambling to come up with rules on how commercial drones can be operated. Observers believe regulators are being caught flat-footed when it comes to potential wireless hacking scenarios.
Hence, companies specializing in wireless network analysis tools are attempting to fill the gap with security measures that could help identify and locate the source of threats, then mitigate their effects via detection tools installed in servers at customers' data centers.
These vendors stress the importance of installing frequently updated real-time security measures against emerging threats like drone hackers. Those patches would normally take weeks to install and configure.
The threat to wireless networks will only grow with the explosion of mobile data delivered by ever increasing numbers of mobile devices that serve as entry points into wireless networks. "Security is going to be more and more of a concern" as network administrators struggle to control mobile devices connecting to corporate or government wireless LANs, warned Milind Bhise, director of product marketing and management at Fluke Networks AirMagnet.
Among other network security products, the company frequently upgrades "dynamic threat signature" models, or rules, for handling newly discovered vulnerabilities. They are used along with its AirMagnet Enterprise servers and sensors installed in data centers to detect and defend against network intrusions, perhaps even emerging vulnerabilities like the wireless signal-sniffing drone hovering outside an office window.
"In effect," added Greg Rayburn, a wireless security analyst with Fluke Networks, "drones are flying network access points" that could be used by hackers to breach corporate networks. Potential hackers could, for example, attach "Wi-Fi pineapples"—small, inexpensive hacking tools that spoof Wi-Fi hotspots—to drones already equipped with several cameras in order to hack in to unsecure networks, Rayburn added.
Those attack scenarios could include attaching a rogue access point or hacking into an enterprise wireless network and stealing data such as credit card information, AirMagnet said.
The threat signature updates, which AirMagnet said are available to current customers, could be used not only to detect a drone-based intrusion but also when the drone is streaming video and which commands the controller is sending.
Along with smartphones, tablets and other devices used by workers to access corporate data, hacker drones could also detect signals being emitted from everything from a Google Glass device and near-field communication chips in smart cards to wireless pacemakers.
These devices are "shouting out information," warned Wilkinson, the security analyst. That information could include unique identifiers like Wi-Fi locations and the Media Access Control addresses for unique devices. Wilkinson said a hacker could then figure out owner information using other emissions such as RFID signals.
Lest these hacking scenarios appear far-fetched, St. Louis police discovered in May that a DJI Phantom II Quadcopter controlled via a Wi-Fi connection had struck the 30th floor of the city's tallest building. The drone was reportedly equipped with an HD camera.



