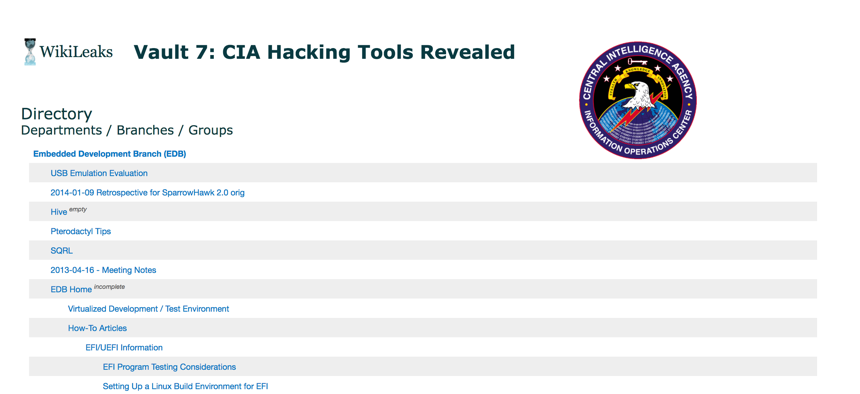
Cropped screenshot from Wikileaks (https://wikileaks.org/ciav7p1/cms/index.html), March 7, 2017.
CIA Claims No Wrongdoing As Wikileaks Claims to Publish Thousands of Agency Files
The group says the 8,000-plus files detail the existence and function of key hacking tools.
Note: This article has been updated to note a CIA statement.
The CIA on Tuesday had no comment about Wikileaks’ claim to have revealed the existence and function of key hacking tools in a document dump that the group calls “the largest intelligence publication in history.” On Wednesday evening they provided an expanded response, claiming no wrongdoing. The response is included below.
In a Tuesday statement on its site, Wikileaks officials claimed to have obtained and posted “8,761 documents and files from an isolated, high-security network situated inside the CIA's Center for Cyber Intelligence in Langley, Virgina” [sic]. The organization said the trove revealed that the spy agency can read encrypted messages sent through popular apps such as Facebook-owned Whatsapp, popular in the Ukrainian military; Signal, a favorite of journalists, dissidents and some in the intelligence community; Telegram, used by jihadists and others; and Confide, popular among Trump administration leakers.
Some cybersecurity researchers immediately called the claims uncorroborated and misleading. It has long been the case that hackers who gain physical access to a phone, for example, may be able to read text written in various messaging apps. It's hard to tell whether the tools described in the dump would allow a spy to enter your phone from anywhere.
First, this appears to be about tools that target selected end users by compromising their phones, not that break the crypto generally. (2/)
— matt blaze (@mattblaze) March 7, 2017
They urged users to remain calm, and not to take the Wikileaks post as a reason to abandon the use of encrypted messaging apps.
That's not what it says. Not about Signal. If your phone is hacked, *nothing* is foolproof. Iphones are hardest to hack. Androids easiest. https://t.co/GwKDO0lxox
— Zeynep Tufekci (@zeynep) March 7, 2017
Among other purported revelations, Wikileaks said, the documents show that the CIA and British intelligence outfit MI5 developed malware to listen in on the microphones in Samsung smart TVs; and that the U.S. consulate in Frankfurt, Germany, has become a hub for U.S. signals intelligence agents and engineers traveling under diplomatic passports.
Shocked. https://t.co/O1V9spdL7T
— the grugq (@thegrugq) March 7, 2017
In their post, the group said they had redacted some of the posted emails and communications to avoid “the ‘distribution of 'armed' cyberweapons until a consensus emerges on the technical and political nature of the CIA's program and how such 'weapons' should analyzed, disarmed and published.”
The group also hinted that the documents were leaked by a source inside the agency. “The source wishes to initiate a public debate about the security, creation, use, proliferation and democratic control of cyberweapons,” they wrote. “The source details policy questions that they say urgently need to be debated in public, including whether the CIA's hacking capabilities exceed its mandated powers and the problem of public oversight of the agency.”
Asked for comment, CIA spokesperson Jonathan Liu said, “We do not comment on the authenticity or content of purported intelligence documents.”
Update: On Wednesday evening, Dean Boyd, the director of public affairs for the CIA, wrote back to Defense One and other reporters with an expanded statement:
“We have no comment on the authenticity of purported intelligence documents released by Wikileaks or on the status of any investigation into the source of the documents. However, there are several critical points we would like to make: CIA’s mission is to aggressively collect foreign intelligence overseas to protect America from terrorists, hostile nation states and other adversaries. It is CIA’s job to be innovative, cutting-edge, and the first line of defense in protecting this country from enemies abroad. America deserves nothing less. It is also important to note that CIA is legally prohibited from conducting electronic surveillance targeting individuals here at home, including our fellow Americans, and CIA does not do so. CIA’s activities are subject to rigorous oversight to ensure that they comply fully with U.S. law and the Constitution. The American public should be deeply troubled by any Wikileaks disclosure designed to damage the Intelligence Community’s ability to protect America against terrorists and other adversaries. Such disclosures not only jeopardize US personnel and operations, but also equip our adversaries with tools and information to do us harm.”
On Thursday morning, Boyd added to the Wednesday statement: "As we’ve said previously, Julian Assange is not exactly a bastion of truth and integrity. Despite the efforts of Assange and his ilk, CIA continues to aggressively collect foreign intelligence overseas to protect America from terrorists, hostile nation states and other adversaries."
Defense One also reached out the office of the National Counterintelligence Executive, which is in charge of responding to releases or disclosures of U.S. intelligence assets, methods or products.
In September, we interviewed the National Counterintelligence Executive himself, William Evanina, who described how hard it remains to thwart insiders who want to leak data.
“To no extent are we capable of stopping someone from doing damage who wants to. It’s not possible,” said Evanina,. “The same way you can’t stop someone from starting a fire who wants to be an arsonist.”
Still, there is plenty of reason to be skeptical about documents published by Wikileaks — about their veracity, whether they might have been tampered with, who provided them, and so on. Independent research and the intelligence community have determined that Wikileaks has routinely published documents and data given to it by Kremlin-linked intelligence agencies.
If the new Wikileaks dump proves valid, and the source does turn out to be a mole inside the CIA, then it will be the second release of information about critical intelligence tools in a year by an insider. On Aug. 27, NSA contractor Harold Martin III was arrested for hoarding agency documents. He is suspected of offering NSA tools for sale.
The group claims that its revelations are just scratching the surface.
“Wikileaks has intentionally not written up hundreds of impactful stories to encourage others to find them and so create expertise in the area for subsequent parts in the series. They're there. Look. Those who demonstrate journalistic excellence may be considered for early access to future parts,” they write.
Russia?
To attribute the document drop to pure altruism on the part of Wikileaks would probably be a mistake. In fact, it seems to be setting the stage for an organized communications campaign to discredit the intelligence community assessment on the DNC hack, which would suggest the source could have been the Kremlin (at very least, they were quick to capitalize on the development.) Both the intelligence community and private cyber security researchers have determined that Russian actors stole both the DNC and John Podesta emails published to Wikileaks.
A portion of the Wikileaks statement released today reads: "The CIA's Remote Devices Branch's UMBRAGE group collects and maintains a substantial library of attack techniques 'stolen' from malware produced in other states including the Russian Federation...With UMBRAGE and related projects the CIA cannot only increase its total number of attack types but also misdirect attribution by leaving behind the "fingerprints" of the groups that the attack techniques were stolen from."
Pro-Russian information sites and trolls were quick to notice the claim.
New Leaks Confirm: CIA Posed as ‘Russian Hackers’ https://t.co/iZWF6sEWf8 pic.twitter.com/JadtKE3jl9
— Russia Insider (@RussiaInsider) March 7, 2017
CIA uses techniques to make cyber attacks look like they originated from enemy state. It turns DNC/Russia hack allegation by CIA into a JOKE
— Kim Dotcom (@KimDotcom) March 7, 2017
Some alternative right conservative outlets such as Breitbart were quick to follow the trend.




