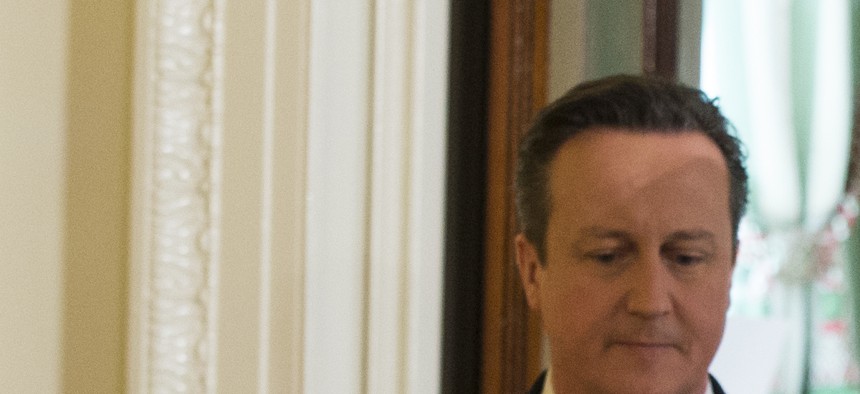
President Barack Obama and British Prime Minister David Cameron arrive for a joint news conference in the East Room of the White House, on Jan. 16, 2015. Evan Vucci/AP
US, UK Establish a Joint Hacker A-Team To Conduct Cyber War Games
The U.S. and U.K. discuss terrorism and cyber safety and unveil new collaborative steps. By Patrick Tucker
The White House on Friday unveiled a series of steps to increase co-operation between the United States and the United Kingdom in combating cyber threats. Those steps include better threat information sharing and the creation of a new joint cyber task force.
The U.S. and U.K. already collaborate with one another and with many other countries on cyber defense issues through the Computer Emergency Readiness Team program. Today, President Barack Obama and British Prime Minister David Cameron announced the formation of a “joint cell,” that will have a physical presence in both countries and will bring together Internet security experts from the United Kingdom’s Government Communications Headquarters, GCHQ, Security Service, MI5, the National Security Agency, NSA, and the Federal Bureau of Investigation.
“The cell, which will allow staff from each agency to be co-located, will focus on specific cyber defense topics and enable cyber threat information and data to be shared at pace and at greater scale,” according to a White House statement.
The cell will conduct cyber war games in the spring, simulating attacks on the financial sector.
The announcement comes at the end of a week in which the White House unveiled a variety of proposals in anticipation of the State of the Union next week to strengthen cyber defenses.
Among the bevy of ideas that the White House offered up, an update to its 2011, Cybersecurity Legislative Proposal, emphasizing again information sharing, but this time between the private sector and government. The proposal includes liability protections for companies that choose to share with the Department of Homeland Security, DHS, information about threats that they are facing, intrusion attempts, broadly defined anomalous user behavior, or patterns that could indicate a cyber attack or intrusion attempt.
“Specifically, the proposal encourages the private sector to share appropriate cyber threat information with the Department of Homeland Security’s National Cybersecurity and Communications Integration Center (NCCIC), which will then share it in as close to real-time as practicable with relevant federal agencies and with private sector-developed and operated Information Sharing and Analysis Organizations (ISAOs) by providing targeted liability protection for companies that share information with these entities,” according to a statement.
The moves were welcomed by cyber hawks in Washington this week.
“A cyber-sharing bill that gives liability protection? What a great idea!” former House Intelligence Committee Chairman Rep. Mike Rogers, R-Mich., said at a Bipartisan Policy Center event on Thursday. Rogers was making light of the fact that the White House proposal shares much common with his own Cyber Intelligence Sharing and Protection Act, CISPA, which he introduced last year and which stalled in the Senate.
“We’re a long way from a cyber-sharing piece of legislation,” he said. “I had a very senior senator tell me that they still had to get to 60 votes….we’re still far away from making it work.”
Critics of the new White House proposal, such as Mark Jaycox of the Electronic Frontier Foundation, have said that giving the companies more liability protection to share private user or customer data with the government will hurt privacy. Furthermore, additional protections for companies aren’t necessary since companies can already share data related to cyber threats though Information Sharing and Analysis Centers (ISACs) and DHS's Enhanced Cybersecurity Services.
“While the administration information sharing proposal may have better privacy protections than dangerously drafted bills like CISPA, we think the initial case for expanding information sharing requires much less secrecy about how intelligence and law enforcement agencies collect and use data on our networks.” Jacobs said in a statement.
The announcements today comes on the heels of two new high profile hacks, where the Twitter accounts of UPI and the New York Post were briefly taken over by groups who posted, erroneously, that the United States had launched a war against China.
It’s been quite a week for British Prime Minister David Cameron. In addition to announcing the formation of the cyber cell, he had a meeting with Obama Friday morning where he asked him to block companies like Apple, Facebook and Google from rolling out encryption services to users, which would allow users to communicate with one another more securely but which the British government claims could hurt intelligence collection.
A U.K. government official, speaking to The Guardian, said: “The prime minister’s objective here is to get the U.S. companies to cooperate with us more, to make sure that our intelligence agencies get the information they need to keep us safe. That will be his approach in the discussion with President Obama – how can we work together to get them to cooperate more, what is the best approach to encourage them to do more.”
The president signaled that he was at least open to the argument. “We've been in dialogue with companies and have systematically worked through ways in which we can meet legitimate privacy concerns, but also meet the very real concerns that David identified and my FBI Director Jim Comey identified.”
As Defense One has previously reported, FBI Director James Comey has been lobbying the White House and Congress to stop Apple and Google from offering encryption to users.
Cameron has suggested that allowing consumers to encrypt messages on their phones and computers would give terrorists a “safe place” to plan and coordinate operations.
“We're not asking for back doors. We have -- we believe in very clear front doors through legal processes that should help to keep our country safe. And my only argument is that as technology develops, as the world moves on, we should try to avoid the safe havens that could otherwise be created for terrorists to talk to each other,” he said.
Blocking encryption may or may not make the U.S. and the U.K. more safe from groups like the Islamic State, but according to a report by the United States National Intelligence Council, it likely won’t make us safer from cyber threats. The report highlights what the broader technology community has always known, that encryption is “the best” defense against data theft. And data theft, which can include stolen passwords to social networking sites or other sensitive user behavior, is often a key predictor of larger cyber attacks or incident of theft to come.
NEXT STORY: US, Britain Mull Cross-Border Cyber Defense