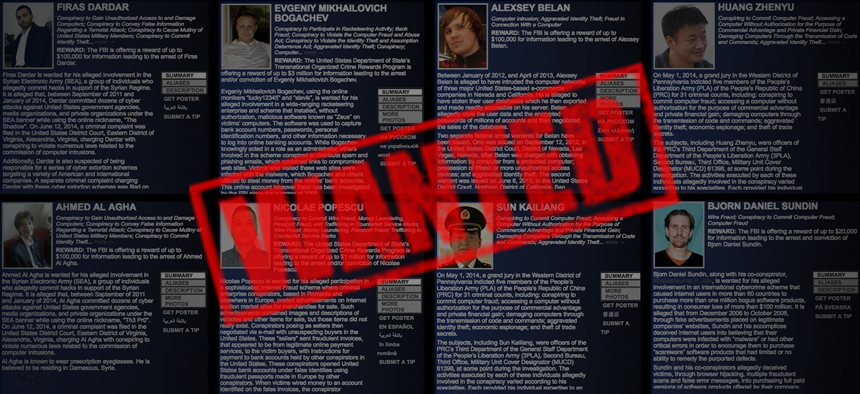
Photos/profiles via the FBI
Are These Syrian Hackers Cyber Warriors, or Just Thieves?
The FBI added two Syrian hackers to its most-wanted list for cybercriminals, a project that's only been running since 2013 and includes individuals from China, Russia and Eastern Europe.
In late April 2013, a tweet from the Associated Press claimed that a pair of explosions at the White House had injured President Barack Obama. Markets reacted nearly instantly, sending stocks plunging. But when, a short time later, Press Secretary Jay Carney told reporters there was no explosion, the market quickly righted itself.
The news organization’s Twitter account was hacked, it turned out. A group calling itself the Syrian Electronic Army claimed credit. In only a few minutes, their rogue tweet demonstrated the market-moving power of 140 characters sent from a credible source.
The Syrian Electronic Army has also defaced websites belonging to the U.S. Marines, Harvard University, and Human Rights Watch, as well as websites and Twitter feeds of other major news organizations like the BBC, CNN, and The Washington Post . The group’s members remained anonymous, going by pseudonyms like “The Shadow” and “The Pro.”
But on Tuesday, the Justice Department revealed the identity of three members of the group, charging them with computer hacking and placing two of them on the FBI’s “Cyber’s Most Wanted” list. The FBI is offering a $100,000 bounty for information leading to their arrest.
Read more: Hacker May Have Punched Through FBI Cyber Security With One Phone Call
Read more: US Still Doesn’t Know Who’s In Charge of What If Massive Cyber Attack Strikes Nation
Read more: Behind the Air Force’s Fast-Growing Cyber Research Budget
The newest additions bring the three-year-old “ Cyber’s Most Wanted ” list to 19 members. The list includes 5 members of China’s People’s Liberation Army and an assortment of hackers from Eastern Europe and Russia.
The most recent inductees are young Syrians: 22-year old Ahmad Umar Agha, known as “The Pro”; 27-year-old Firas Dardar, known as “The Shadow.” The FBI also brought charges against 36-year-old Peter Romar, who it says is based in Germany.

Ahmad Umar Agha, left, and Firas Dardar (FBI)
That Agha and Dadar were able to sow such chaos from behind their laptops in a country in the throes of a civil war illustrates the Internet’s power to democratize conflict. Oceans can’t protect the U.S. from cyberattacks, most of which originate in countries that are (at least technically) at peace with America. And compared to capers like a massive Chinese heist of personal data from the Office of Personnel Management, the Syrians’ attacks were mild.
FBI agents filed two criminal complaints that implicate the three men in 2014 and 2015, but the charges were only unsealed on Tuesday. They paint a picture of a long-running series of targeted online attacks on the U.S. government, media organizations, and private companies worldwide.
The Syrian Electronic Army says it supports the government of Syrian President Bashar al-Assad, and some of its actions appeared to be retaliation for American support of rebel groups fighting against Assad’s regime. Those included a series of unsuccessful attacks on the White House, where group members posed as White House employees to try and steal login credentials for a White House Twitter account. In a separate attack, they redirected people attempting to visit the website marines.com to a page that encouraged American soldiers to “refuse [their] orders.” (That particular bit of mischief earned Agha and Dardar a charge of attempting to cause mutiny of the U.S. armed forces.)
But other online attacks were engineered to maximize personal gain, according to the Justice Department complaint. The FBI alleges that Agha and Dardar hacked into companies in Europe, Asia, and U.S., threatening to delete or sell their private data unless paid a ransom. The FBI investigation identified 14 victims, from whom the attackers attempted to extract a total of $500,000. The complaint said the hackers weren’t always paid in full.
The FBI found the hackers’ identities by obtaining search warrants for their Google and Facebook accounts. The men often used Gmail accounts to threaten and extort money from their victims, investigators said.
In a statement issued Tuesday, Assistant Attorney General John Carlin acknowledged the complicated nature of the case his department unsealed. “The allegations in the complaint demonstrate that the line between ordinary criminal hackers and potential national security threats is increasingly blurry,” Carlin said.
Beyond offering rewards for their capture, the FBI has limited options to bring the Syrian hackers in. But that’s not to say the U.S. takes the threat of hackers abroad lightly. In August, a targeted drone strike killed Junaid Hussain , a British national in his twenties affiliated with the Islamic State who had allegedly hacked U.S. military systems and contributed to the group’s online defenses.
Hussain had attracted the interest of U.S. officials not just for his hacking prowess, but also for his efforts to recruit others and his apparent leadership role in the Islamic State.
The Syrian hackers are less likely to find themselves in the crosshairs of a military drone than an IS operative—and besides, if counterterrorism officials wanted these men dead, they probably wouldn’t wait for the FBI to unseal years-long investigations into their actions.
But there’s no question that hackers abroad who target the U.S. are being closely followed by law enforcement here. Malicious code can be as big a threat as bullets and missiles to national security, and are much more easily delivered.



